BLACK HAT USA: The adoption of double-extortion attacks against companies in ransomware campaigns is a rising trend in the space, researchers warn.
Ransomware variants are typically programs that aim to prevent users from accessing systems and any data stored on infected devices or networks. After locking victims out, files and drives will often be encrypted — and in some cases, backups, too — in order to extort a payment from the user.
Today, well-known ransomware families include WannaCry, Cryptolocker, NotPetya, Gandcrab, and Locky.
Ransomware now seems to make the headlines month-on-month. Recently, the cases of Colonial Pipeline and Kaseya highlighted just how disruptive a successful attack can be to a business, as well as its customers — and according to Cisco Talos, it’s likely to only become worse in the future.
In 1989, the AIDS Trojan — arguably one of the earliest forms of ransomware — was spread through floppy disks. Now, automated tools are used to brute-forcing internet-facing systems and load ransomware; ransomware is deployed in supply-chain attacks, and cryptocurrencies allow criminals to more easily secure blackmail payments without a reliable paper trail.
As a global issue and one that law enforcement struggles to grapple with, ransomware operators may be less likely to be apprehended than in more traditional forms of crime — and as big business, these cybercriminals are now going after large companies in the quest for the highest financial gain possible.
At Black Hat USA, Edmund Brumaghin, research engineer at Cisco Secure said the so-called trend of “big game hunting” has further evolved the tactics employed by ransomware operators.
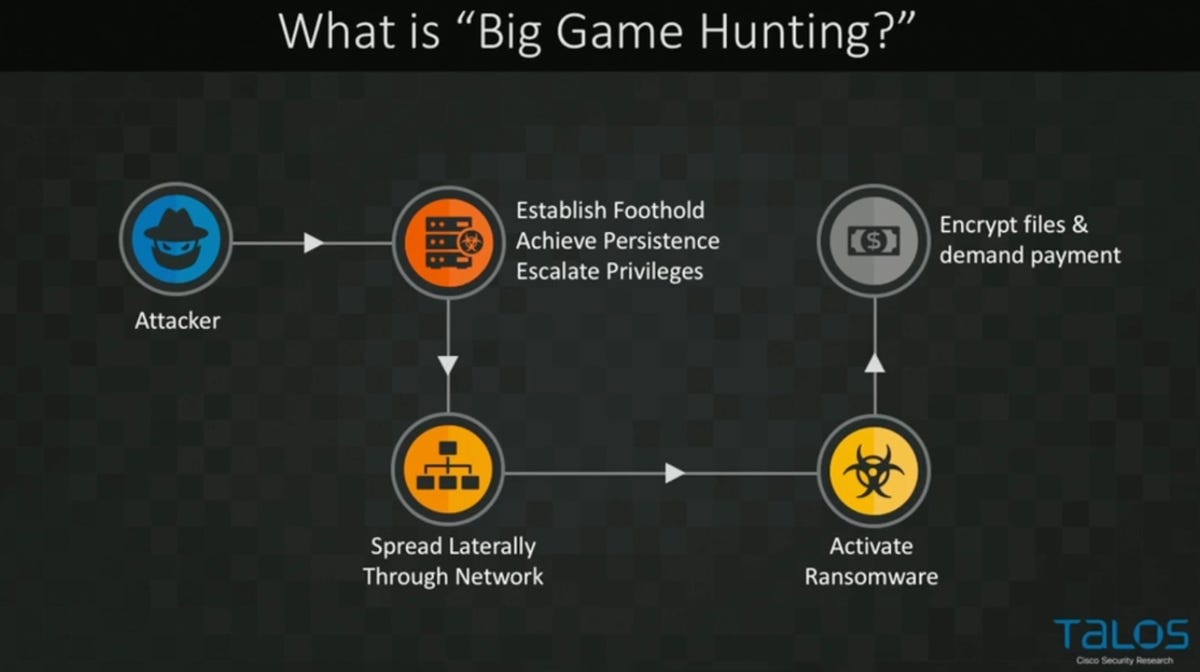
Now big game hunting has gone “mainstream,” Brumaghin says that cyberattackers are not deploying ransomware immediately on a target system. Instead, such as in the example of typical SamSam attacks, threat actors now, more often, will obtain an initial access point through an endpoint and then move laterally across a network, pivoting to gain access to as many systems as possible.
Cisco Talos
“Once they had maximized the percentage of the environment that was under their control, then they would deploy the ransomware simultaneously,” Brumaghin commented. “It’s one of those types of attacks where they know that organizations may be forced to pay out because of instead of a single endpoint being infected, now, 70 or 80 percent of server-side infrastructure is being impacted operationally at the same time.”
After a victim has lost control of their systems, they are then faced with another problem: the emerging trend of double-extortion. While an attacker is lurking on a network, they may also rifle through files and exfiltrate sensitive, corporate data — including customer or client information and intellectual property — and they will then threaten their victims with its sale or a public leak.
“Not only are you saying you only have X amount of time to pay the ransom demand and regain access to your server, if you don’t pay by a certain time, we’re going to start releasing all of this sensitive information on the internet to the general public,” Brumaghin noted.
This tactic, which the researcher says “adds another level of extortion in ransomware attacks,” has become so popular in recent years that ransomware operators often create ‘leak’ sites, in both the dark and clear web, as portals for data dumps and in order to communicate with victims.
According to the researcher, this is a “one-two-punch” method that is made worse now that ransomware groups will also employ Initial Access Brokers (IABs) to cut out some of the legwork required in launching a cyberattack.
IABs can be found on dark web forums and contacted privately. These traders sell initial access to a compromised system — such as through a VPN vulnerability or stolen credentials — and so attackers can bypass the initial stages of infection if they are willing to pay for access to a target network, saving both time and effort.
“It makes a lot of sense from a threat actor’s perspective,” Brumaghin said. “When you consider some of the ransom demands we’re seeing, in a lot of cases, it makes sense to them instead of trying to go through all the effort [..] they can simply rely on initial access brokers to give them access that has already been achieved.”
Finally, Cisco’s security team has also noted an uptick in ransomware ‘cartels’: groups that sharing information and working together to identify the techniques and tactics that are most likely to result in revenue generation.
Brumaghin commented:
“We’re seeing a ton of new threat actors begin to adopt this business model and we continue to see new ones emerge, so it’s something organizations really need to be aware of.”
Previous and related coverage
Have a tip? Get in touch securely via WhatsApp | Signal at +447713 025 499, or over at Keybase: charlie0
[ad_2]
Source link
Is your business effected by Cyber Crime?
If a cyber crime or cyber attack happens to you, you need to respond quickly. Cyber crime in its several formats such as online identity theft, financial fraud, stalking, bullying, hacking, e-mail fraud, email spoofing, invoice fraud, email scams, banking scam, CEO fraud. Cyber fraud can lead to major disruption and financial disasters. Digitpol can assist with all stages of cyber related incidents.
Contact Digitpol’s hotlines or respond to us online.
ASIA +85239733884
Europe +31558448040
UK +44 20 8089 9944

