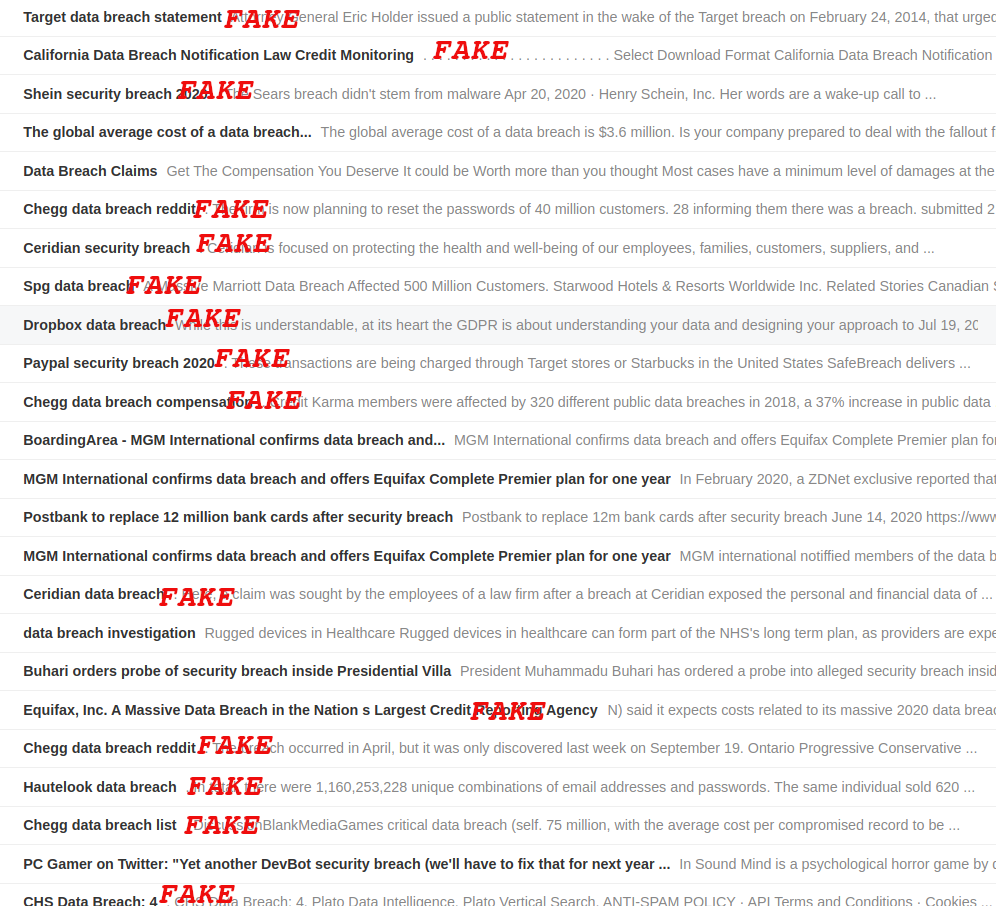
Fraudsters recently have started to push fake data breach notifications for big company names to distribute malware and scams. They’re mixing black SEO, Google Sites, and spam pages to direct users to dangerous locations.
Google Alerts helps to spread these fake notifications as the service monitors search results for user-defined keywords. Scammers created pages or used compromised websites to combine “data breach” with well-known brands.
Fake security incidents
BleepingComputer has seen fake breach notifications for companies like Chegg, EA, Canva, Dropbox, Hulu, Ceridian, Shein, PayPal, Target, Hautelook, Mojang, InterContinental Hotels Group, and Houzz. These companies have suffered a data breach at one point in the past.
Following any of these links picked up by Google Alerts ends with landing on pages with fake giveaways, download offers for unwanted extensions and malware.
To make it harder to detect their malicious behavior, navigating to the pages directly may not reveal the true nature of the campaign.
Users may instead see a “page not found” error or a text specifically created to promote a fake data breach.
BleepingComputer found on a hacked website a directory (penartdesigner[.]com/ifcemva/) with about 2,000 text files like the one above with specific keywords to promote a topic in search results.
All but one entry were last modified this year starting June 11, the vast majority on June 15. The timestamp for the exception, which has the oldest date, is July 31, 2018.

The information in the blobs of text was copied from public sources and covers an extremely wide variety of subjects. Basically, the fraudsters created this portfolio of files from scraping the internet for issues or questions for which users needed an answer.
As for the topics, they are of the most diverse kind. From various software products (note-taking, SDKs, street lighting design, firmware, libraries) and DIY construction projects to oil vapes, canine breeding, hardware issues, and teeth aligners.
Whenever someone searches for a certain topic, the scammer’s results would rank higher in the results and have a better chance of being accessed to start the redirect chain to nasty offers and content.
Apart from using compromised websites, scammers may also set up their own pages. In many cases, they used Google Sites, a tool specifically created for building web pages, to host their content.
Google Alerts links redirect to malware
If you use a Google Alerts or search engine link to arrive at one of these fake data breach sites, the experience is very different compared to going there directly.
Clicking on a Google link redirects users through multiple addresses until the final one is reached. What is shown there depends on the user’s location.
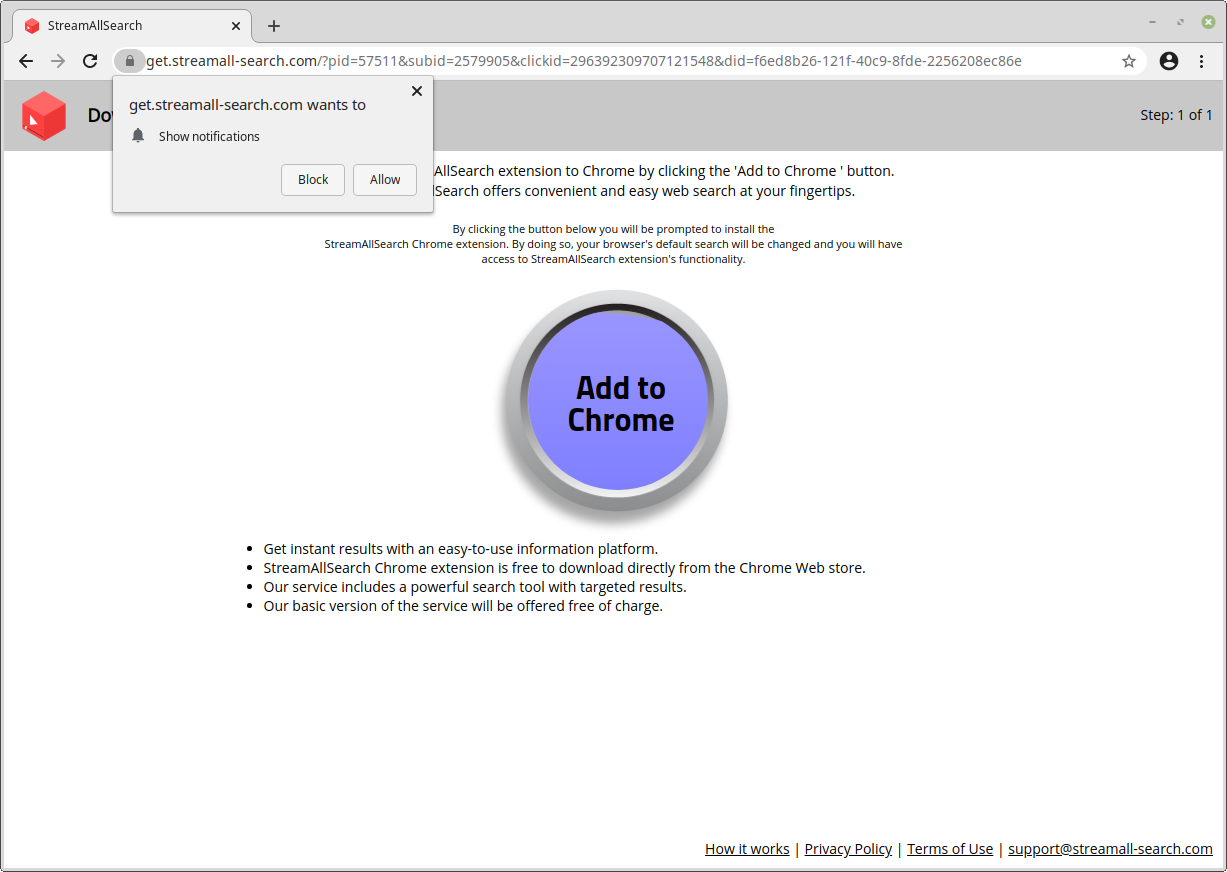
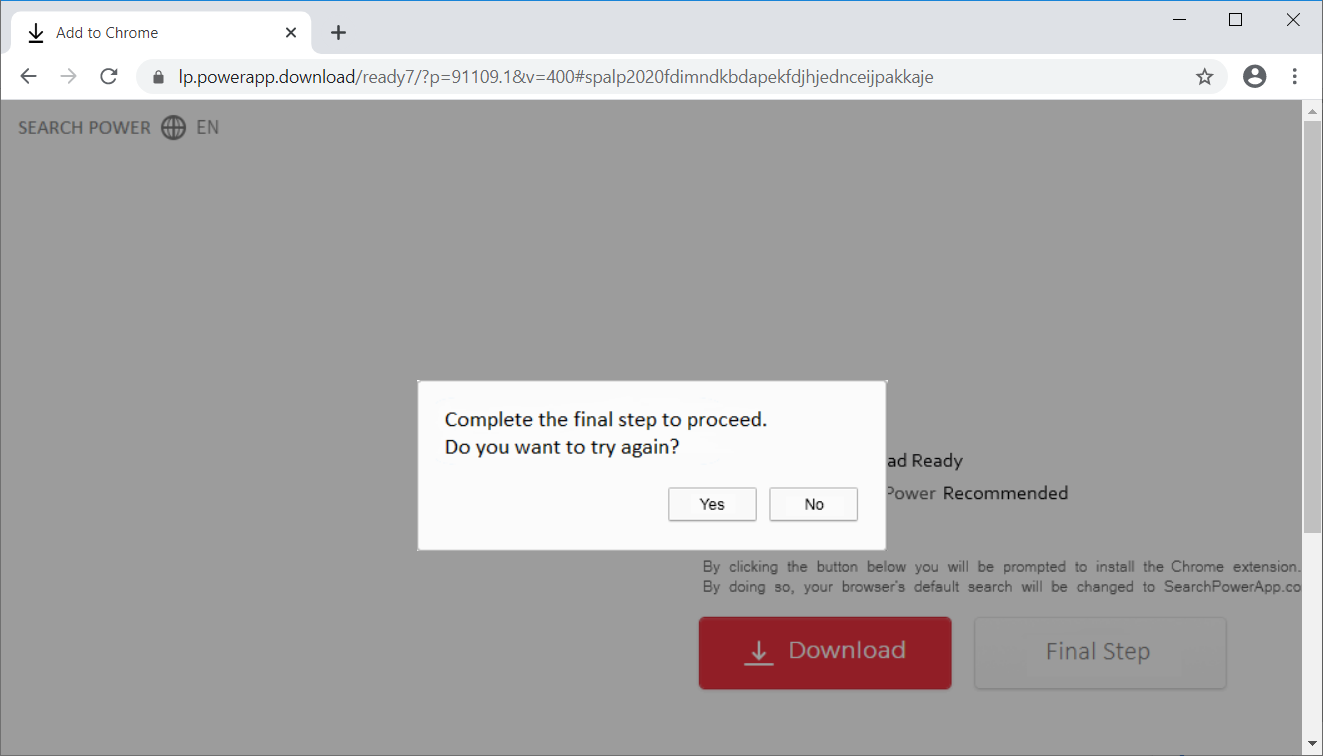
On most occasions, we found that the fraudsters pushed unwanted search-related extensions.
|
|
|
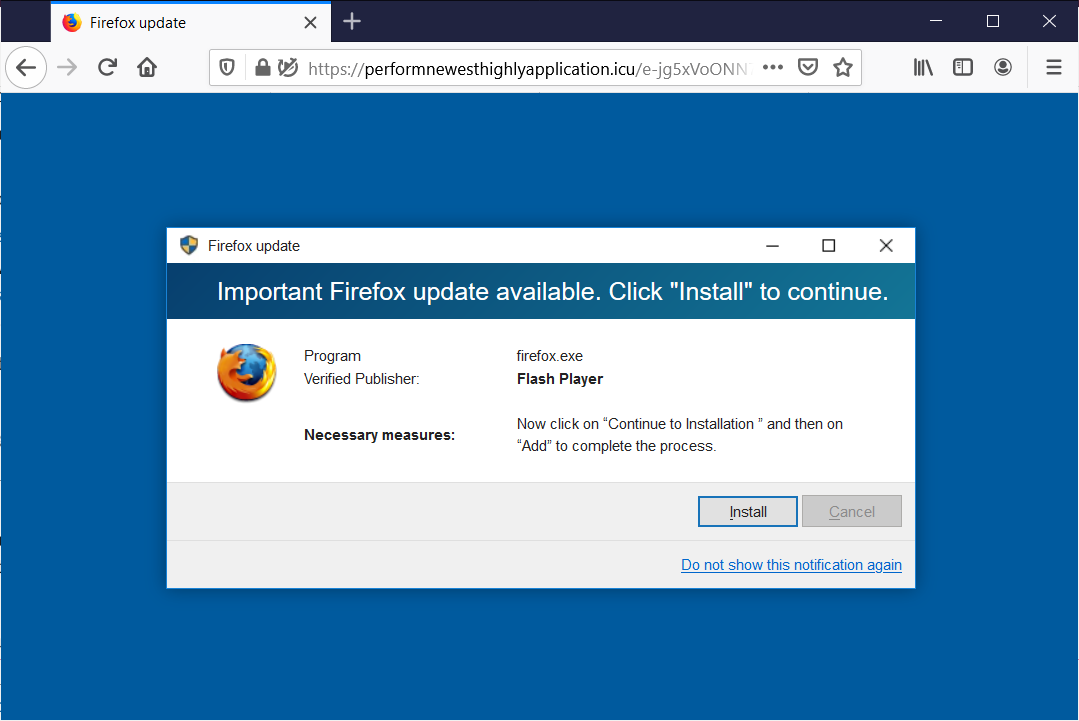
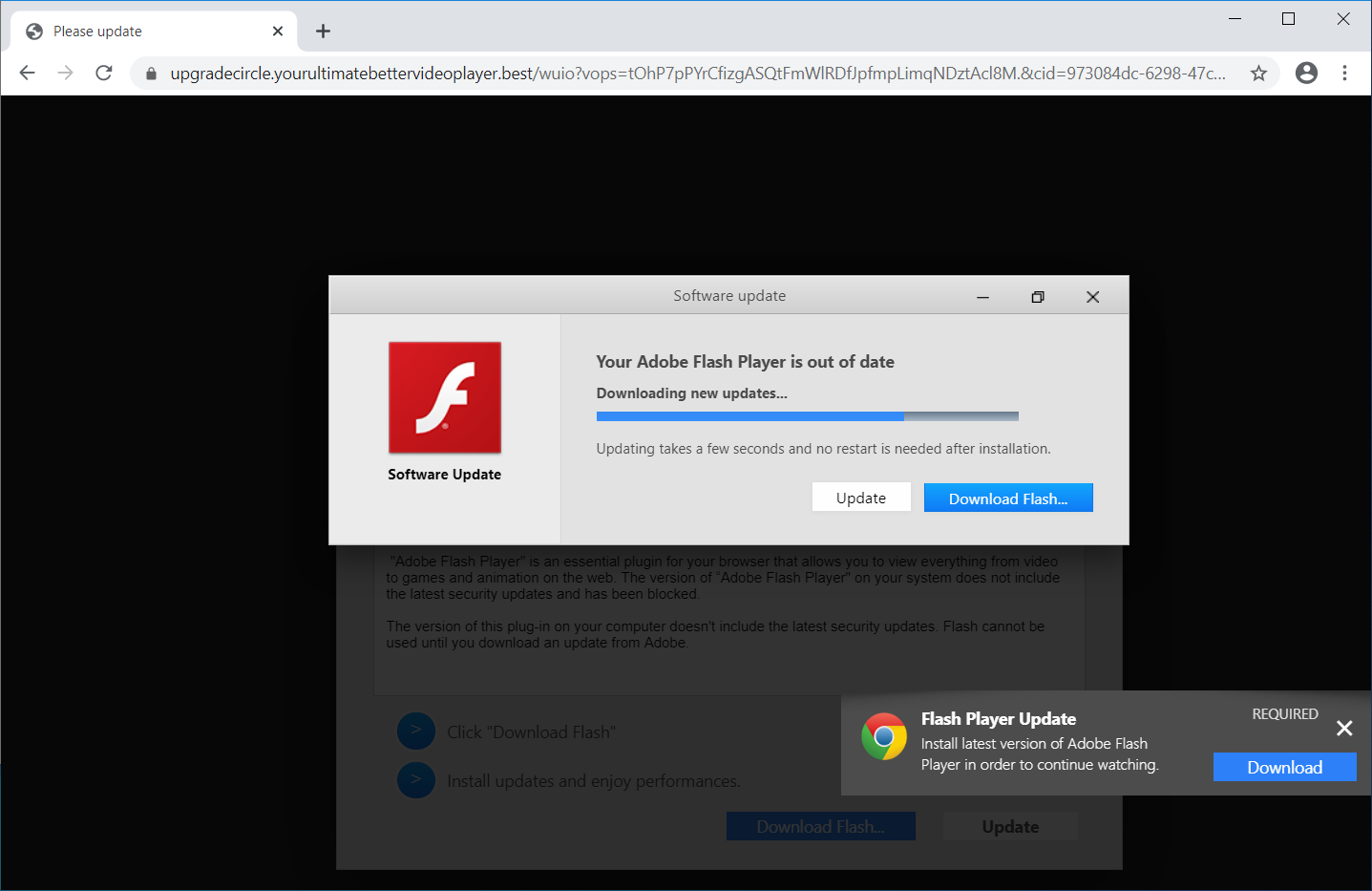
Fake Adobe Flash update notifications were also very common, asking users to install the latest version of the player if they wanted to access the content promised before the redirect.
These fake alerts popped up in both Google Chrome and Mozilla Firefox web browsers. It should be noted that Flash Player will be deprecated in December and current versions of the two browsers no longer support it in the default configuration. Users can still turn it on manually until the software is completely phased out.
|
|
|
We also found that one of the malicious links redirected to a fake giveaway for iPhone 11 devices, claiming that it was set up by Google as part of its “Membership Rewards” program.
To make this offer more believable, the notification also claimed that the gift was “exclusively and only for Verizon Fios users” in the region identified for the user. Getting the gift, though, requires completing a survey, which is how the scammers make their money.
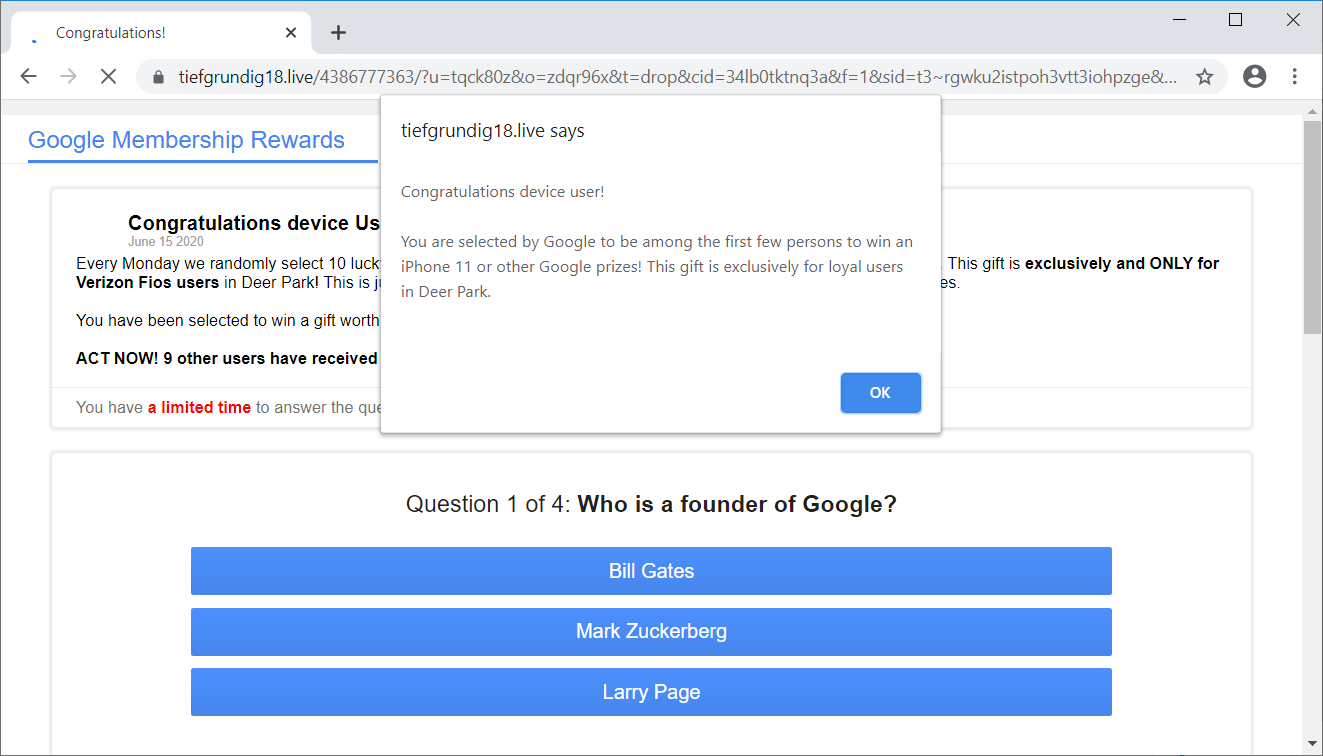
If surveys may not cause much damage and only waste a user’s time, a browser extension scam can pose a serious risk to your browsing privacy and malware can also be delivered using this method.
Typically, extensions can read the pages you access and even modify them; for this, legitimate ones approved in official repositories inform the user and ask for their explicit consent. A malicious extension, though, can skip this step and collect a user’s interests and sell them to interested parties.
Using spam pages to redirect users to pages that pose a risk is not a new thing. BleepingComputer reported in September last year that scammers used the same tactic to target users looking for ransomware decryptors.
[ad_2]
Source link
Is your business effected by Cyber Crime?
If a cyber crime or cyber attack happens to you, you need to respond quickly. Cyber crime in its several formats such as online identity theft, financial fraud, stalking, bullying, hacking, e-mail fraud, email spoofing, invoice fraud, email scams, banking scam, CEO fraud. Cyber fraud can lead to major disruption and financial disasters. Contact Digitpol’s hotlines or respond to us online.
Digitpol is available 24/7.
Email: info@digitpol.com
ASIA +85239733884
Europe +31558448040
UK +44 20 8089 9944